The GLADIO CODE Has Been Broken, NATO’s Terror Network Shattered (1)
G-10 reveals what no one has ever disclosed before

The following intelligence report on NATO’s Operation Gladio was filed by former French undercover agent and computer scientist Marc Delantre.
The purpose of this report is to familiarize the reader with the super-secret “signal” that was actually created by the operational head of Gladio (now known as G-10) to communicate with M. Delantre. As difficult as this might be to comprehend, the hard digital evidence provided by G-10 proves conclusively that this ongoing signaling initiative has been taking place throughout most of 2018.
Only by reading this extraordinary exposé can anyone begin to see the direct connection between Gladio and a growing number of terrorist operations perpetrated around the world. Were one to dig deeper into each attack, it would become quickly apparent that they each have a unique set of specific objectives as well as serve to advance an underlying global agenda (i.e. New World Order).
What is critical to understand is that alternative media had previously labeled many of the concerned terror attacks as classic Gladio operations. This Gladio branding was done completely independent of and without foreknowledge of Delantre’s accurate analysis posted below.
Once the scientific evaluation of the digital data began to support the existence of a pervasive paradigm of Gladio terror, it became clear that a massive terrorist network has been in place globally over many decades. In fact, virtually every terror attack anywhere in the world today is carried out under the rubric of NATO’s Operation Gladio. This is precisely why NATO has been renamed by the Alt Media as the North Atlantic Terrorist Organization.
There are very good reasons why both NATO and Operation Gladio headquarters are both located in Brussels, Belgium. Although it has been officially stated that Gladio was dissolved a number of years ago, it was not. In point of fact, Gladio is more active than it has ever been as seen by the never-ending and ever-intensifying reign of terror across the planet. The fake War on Terror was in reality initiated to provide cover and justification for Gladio operations executed around the globe.
The terrorist attacks of September 11th were a classic Gladio black operation which was coordinated with several intelligence agencies (e.g. the entire U.S. Intelligence Community) and secret services (e.g. MOSSAD) around the world. Prior to 9/11, there were numerous terror operations such as the 1993 World Trade Center bombing that were also perpetrated under the Gladio umbrella.
So far-reaching is Gladio’s influence worldwide that they are the only over-arching organization (along with full C.I.A. support) that can pull off so many terror attacks and never be exposed… until now. What is revealed below is the back story which describes how every Gladio-sponsored attack is now telegraphed via a digital “signal” that contains revealing signatures as they are sent in real-time.
It’s crucial for every resident of planet Earth to understand that Gladio terrorism can show up anywhere, anytime and in any way. So complete is their command and control of this realm that no one is immune to their false flag terror attacks. Hence, everyone ought to have an interest in exposing their game plan once it becomes known. After all, who does not want to prevent the death and destruction that always occurs during and after Gladio black ops?
Truly, there are no NIMBY-s (protesters, coming from the protest sign “Not In My Back Yard”) where it concerns NATO’s Gladio-coordinated terrorism. These state-sponsored terrorist cells operate wherever, whenever and however they so choose to. Given this stark reality, every inhabitant of the planetary civilization ought to pay attention to the messages delivered by G-10.
Just who is G-10? And from where does he issue forth the most radioactive information and ultra-classified data in the world?
The “Gladio Code” has finally been broken. Hence, the global terror matrix has been “shattered” because Gladio’s secret strategy and signature modus operandi have been revealed like never before. Once an insider chose to expose the underbelly of NATO’s Operation Gladio, it has become apparent that virtually all terrorism is state-sponsored and overseen by the Brussels headquarters.
Why Brussels? Because it’s also the Pedogate capital of the world. Not only is the Belgium government completely controlled by the Pedogate control mechanism, so is the NATO leadership and Gladio hierarchy. In this manner, federal governments around the globe are likewise coerced into supporting the worldwide regime of terror that currently afflicts humanity.
Henceforth, the North Atlantic Terrorist Organization will be held responsible for the incessant terrorist attacks. Gladio false flag operations will now be seen as the state-sponsored terrorism that they truly are. Eventually, this grim reality will catch up with those government officials and political leaders who have taken advantage of this transparently fake “War on Terror” to promote the perpetual war economy for the Military-Industrial Complex.
What follows is Marc Delantre’s extraordinary work that exposes Gladio as the killing machine and fear-generating entity it has always been.
Gladio created a signal to communicate with his Messenger, Marc Delantre
Submitted by Marc Delantre
This signal has been created by Gladio to communicate with me, their Messenger. What is this signal?
Even if I did not know yet, I was dealing with Gladio since the summer 2008. Indeed, without knowing it, I was very close of the mastermind of Gladio and he tried to hire me for my computer skills. The French authorities asked me to be their undercover man within this organized crime organization. I did not know at that time that I was facing Gladio. The Mossad exfiltrated me from this situation in 2009 and used me till 2012. In 2013, I tried to denounce everything in Belgium and I had to face Gladio in my home. I have been poisoned two times, but not with the goal of killing me. The head of Gladio did not want to kill me, but only to control me and to push me out of their main area, Belgium. And, indeed, I left my country in 2014 to go in Madagascar.
On September 16, 2014, when I was in Madagascar, the judge in Belgium in charge of my complaint opened by the Belgian Secret Service asked a police commissioner to investigate on my case. Three hours later my computer in Madagascar was seriously attacked and one of my web servers completely disappeared. These destructive Internet attacks lasted 3 weeks and finally that commissioner asked me if I will come back to get an audition for this case. Since they did not want to protect me, I refused, and the judge closed the file at the end of 2014.
The terror attacks in Europe would begin in the first days of 2015.
But Gladio decided at the same time to use me to denounce their activities, but in their way, not in my way. To reach this goal, they needed a very discrete way to communicate with me.
An Internet DDoS (Distributed Denial-of-Service) weapon to communicate with me
Gladio also specializes in the cyber-attacks and Internet weapons. We call this cyber-terrorism. My own story has some links with the birth and the evolution of the most powerful cyber-weapon in the world. In 2012, when the leader of the Mossad agents was taking care of me in Belgium, he died in strange circumstances and then my wife disappeared at the same time. A cyber-terrorist team v-DOS also began their activity in Israel. This team had the specialty to launch DDoS attacks against web servers.
A DDoS attack consists of sending a large volume of data and connections to the same server to take it down. In 2014, the best way to launch a DDoS attack was to use dozens, hundreds or thousands of computers, and to command to these computers to send massive amounts of data and to connect at the same time to a same target. The hackers take the control of these computers through a virus. Everybody has experienced that their favorite site cannot be reachable from time to time. The reason for this can be a DDoS attack.
I don’t know why, but in 2014, when Gladio succeeded in closing the complaint opened with the Belgian Service, this v-DOS team began officially to sell and to launch DDoS attacks on demand, for their customers. When the Belgian authority asked me if I was ready to come back in Belgium, I also received very small DDoS attacks on my web server. They did not attack me, but I understood that these small attacks were a threat, if I planned to enter Belgium.
It was the first time that any organization used a DDoS cyber-weapon to send me a message and I understood its purpose of course. I knew that these very small attacks, without any effects, could also be very destructive if they used their DDoS weapon at a normal level. So, it was already very strange to me that they used a powerful DDoS weapon to message me. Or, that the DDoS attack is fully active and destructive, or that there is no attack at all. So, such level of attack was not an attack at all; rather, it was a way to communicate with me through a specific type of signal.
It was also in 2014 when the flight MH17 had been shot down over the Ukraine that I got the first DDoS “warning” attack for something where I was not involved. I was very surprised, since this DDoS warning was coming from the area of the crash. I made the link and I wrote it. I did not know it at the time, but Gladio saw on my screens that I understood it. So, they probably decided to continue in this way to communicate with me.
In 2015, when I was disconnected sometimes from the Internet for traveling or visiting or because I did not have Internet connection for a while, I again received these DDoS “warnings”. I was not surprised.
In 2016, after the terror attack in Brussels, I decided to send my file to the Belgian Commission for the terror attacks in Brussels. On October 19, I received an email from the office of the top Belgian chief police in Belgium to tell me that they took care of my file sent to this Commission. Again, three hours later, my other web server then disappeared from the web.
I immediately launched another server in the Netherlands and on October 20 my server was already running. On October 21, the USA fell victim to the most powerful cyber-attack ever and the impact point was exactly where my web server was located on October 19 before to be destroyed; the DYN DNS company in Manchester, New Hampshire, U.S.
This was the most powerful attack ever; something like a 9/11 on the Internet. The whole USA was impacted, and the White House was compelled to give a special news conference. Many major US websites went down. The world discovered a new style of DDoS weapon. The target is not attacked by some thousands of infected computers spread over the world, but by 100,000 internet devices spread over the world. These objects are, above all, cameras (CCTV) connected to the Internet and very easy to infect because their access codes are standard. When such a number of infected objects or infected computers are involved this way, it’s called a botnet. The particular virus that was used to infect these Internet devices, especially the CCTV is called Mirai. So, this botnet attacking the USA on October 21, took the name of Mirai botnet.
On December 2016, I saw on my web server in the Netherlands that I received, hundreds of connections per hour, non-stop over several days. I called the FBI and other experts and they confirmed, these connections are coming from Mirai botnet. However, like in 2014, Mirai botnet doesn’t attack me. Thousands of Internet objects of Mirai botnet are connecting on my server every hour, every minute, 24/7. The FBI confirms that my server is not involved in any cyber-terrorism process. My server is definitively not a hub for the Mirai botnet, and they don’t find the reason for these strange connections. I didn’t know yet that it was Gladio, and that they just created with Mirai botnet a frequency on my server to function as a signal. Immediately, I created some Internet applications to follow the changing level of these connections coming from the most powerful Internet weapon in the world.
The signal from Mirai botnet warns me the first terror attack.
On January and February 2017, I see that the level of Mirai botnet connections changes according to what I’m doing and where I’m doing it, even if I don’t have Internet. So Gladio was showing me that they were monitoring me 24/7, even if I didn’t know it was Gladio. I email the FBI, which answers only what they know that my partner and I are being 24/7 monitored. Terrifying it was, even though I did not know yet that I was being monitored by Gladio.
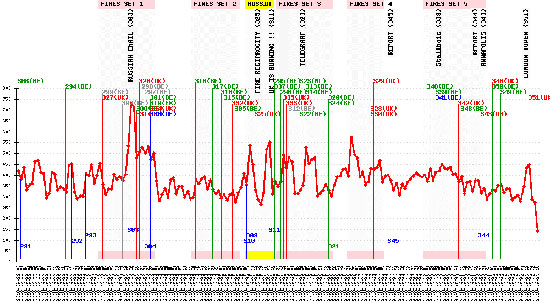
On May 22, 2017, I see that the Mirai botnet suddenly reaches a high-level activity on my server, at more than 1000 connections per hour while its normal level during May 2017 was +/-150 connections per hour. This high activity continues for 4h30 and I try to understand. When it goes back to its normal level, I look to see if I did something wrong to provoke this sudden high level of connections to my server. I did not find anything.
Then I see the news that Donald Trump has just been welcomed to Israel by Benjamin Netanyahu. The Air Force One arrived at 11h02 in the morning, Belgian time, at the airport… and Mirai also reached this high-level activity on my server at 11H02 in the morning!
I understand that Mirai botnet may be warning me of an imminent terrorist attack. I contact the Belgian Terrorist Threat Center, which asks me for a report. I take several hours to write it and shortly after its dispatch, there is the attack in Manchester in the UK at the Arena. There were many deaths including children. Later, the CIA will say that the terrorist who blew himself up was trained in Belgium. I did not know yet that it was really Gladio, but they just warned me of a first terror attack.
Moreover, Gladio leaves nothing to chance and had just launched the 4th terror attack on the 22nd of the month, including the one in Brussels. I see also that this attack occurred in Manchester, UK while Mirai had “celebrated” its birth by its massive attack in the USA on DYN DNS Company, in Manchester, U.S.! Twice, Manchester was hit, so this was not coincidence.
Read the second part of the article
yogaesoteric
December 3, 2018
