WikiLeaks Published ‘Spy Files Russia’ Detailing Russia’s Mass Surveillance System
Perhaps in an attempt to refute recurring allegations that it has traditionally focused on exposing only US state secrets, if not being an outright covert and subversive Moscow front, WikiLeaks released in September (2017) a new cache of documents which it claims detail surveillance apparatus used by the Russian state to spy on internet and mobile users. It’s the first time the organization has leaked material directly pertaining to the Russian state.
The full data dump can be found here.
In its summary of the cache of mostly Russian-language documents, WikiLeaks claims they show how a long-established Russian company which supplies software to telecommunication companies is also installing infrastructure – with the government’s blessing – that enables Russian state agencies to tap into, search and spy on citizens’ digital activity, suggesting a similar state-funded mass surveillance program to the one utilized by the US’ NSA or by GCHQ in the UK (both of which were detailed in the 2013 Snowden disclosures).
And speaking of, shortly following the publication, another famous whistleblower, one also exiled and currently residing in Russia, Edward Snowden, tweeted “Plot twist: @WikiLeaks publishes details on Russia’s increasingly oppressive internet surveillance industry.”

To be sure, arguments have already broken out on Twitter suggesting that WikiLeaks/Assange is trying to deflect from charges that it is a front for the Kremlin by finally dumping something on Russia. Making matters more complicated, it’s not possible at this point to verify the value or veracity of this WikiLeaks document release.
The documents published on September 19 by WikiLeaks (there were just 34 “base documents” in this leak at the date) relate to a St. Petersburg-based company, called Peter-Service, which it claims is a contractor for Russian state surveillance. According to Tech Crunch, the company was set up in 1992 to provide billing solutions before going on to become a major supplier of software to the mobile telecoms industry.
WikiLeaks writes: “The technologies developed and deployed by PETER-SERVICE today go far beyond the classical billing process and extend into the realms of surveillance and control. Although compliance to the strict surveillance laws is mandatory in Russia, rather than being forced to comply PETER-SERVICE appears to be quite actively pursuing partnership and commercial opportunities with the state intelligence apparatus.
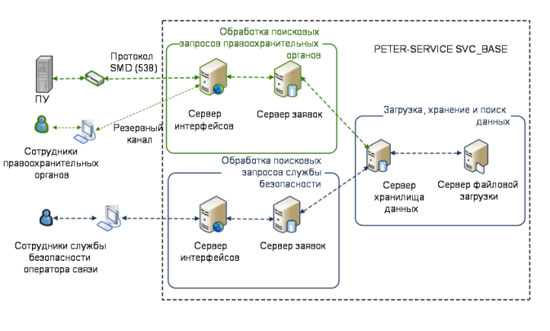
As a matter of fact PETER-SERVICE is uniquely placed as a surveillance partner due to the remarkable visibility their products provide into the data of Russian subscribers of mobile operators, which expose to PETER-SERVICE valuable metadata, including phone and message records, device identifiers (IMEI, MAC addresses), network identifiers (IP addresses), cell tower information and much more. This enriched and aggregated metadata is of course of interest to Russian authorities, whose access became a core component of the system architecture.”
One of WikiLeaks’ media partners for the release, the Italian newspaper La Repubblica reports that the documents cover “an extended timespan from 2007 to June 2015”, and describes the contents as “extremely technical”. It also caveats that the documents do not mention Russia’s spy agency, the FSB, but rather “speak only of state agencies”, a formula it asserts “certainly includes law enforcement, who use metadata for legal interception”. It also says the documents do “not clarify what other state apparatus accesses those data through the solution of the St. Petersburg company”.
WikiLeaks says that under Russia law operators must maintain a Data Retention System (DRS) which can store data for up to three years. La Repubblica reports that Peter-Service’s DRS stores telephone traffic data and “allows Russian state agencies to query the database of all stored data in search of information” – which it specifies can include calls made by a certain telephone company’s customer; payment systems used; the cell phone number to which a user is calling.
“The manuals published by WikiLeaks contain the images of interfaces that allow you to search within these huge data fields, so access is simple and intuitive”, it adds.
Some technical details:
– According to WikiLeaks, Peter-Service’s DRS solution can handle 500,000,000 connections per day in one cluster. While the claimed average searches time for subscriber related-records from a single day is ten seconds. “State intelligence authorities use the Protocol 538 adapter built into the DRS to access stored information,” it adds.
– Peter-Service has also apparently developed a tool called TDM (Traffic Data Mart), which allows the database to be queried to determine “where users’ data traffic is stored in order to understand visited sites, forums, and social media”, as well as how much time is spent on a certain site and the electronic device used to access it.
– WikiLeaks describes TDM as “a system that records and monitors IP traffic for all mobile devices registered with the operator”, and says it maintains a list of categorized domain names – “which cover all areas of interest for the state. These categories include blacklisted sites, criminal sites, blogs, webmail, weapons, botnet, narcotics, betting, aggression, racism, terrorism and many more”.
“Based on the collected information the system allows the creation of reports for subscriber devices (identified by IMEI/TAC, brand, model) for a specified time range: Top categories by volume, top sites by volume, top sites by time spent, protocol usage (browsing, mail, telephony, bit torrent) and traffic/time distribution”, it adds.
WikiLeaks points to a 2013 Peter-Service slideshow presentation (it says this also appears to be publicly available on the company’s website), which it claims is targeted not at telco customers but at state entities such as Russia’s FSB and Interior Ministry (despite this document apparently being in the public domain) — in which the company focuses on a new product, called DPI*GRID; which it says is a hardware device for Deep Packet Inspection that takes the form of “black boxes” apparently able to handle 10Gb/s traffic per unit.
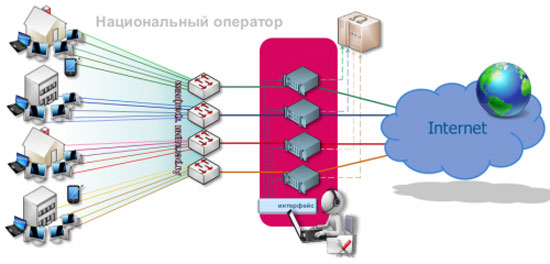
WikiLeaks adds that “the national providers are aggregating Internet traffic in their infrastructure and are redirecting/duplicating the full stream to DPI*GRID units. The units inspect and analyze traffic (the presentation does not describe that process in much detail); the resulting metadata and extracted information are collected in a database for further investigation. A similar, yet smaller solution called MDH/DRS is available for regional providers who send aggregated IP traffic via a 10Gb/s connection to MDH for processing.”
WikiLeaks also makes a point of noting that the presentation was written “just a few months after Edward Snowden disclosed the NSA mass surveillance program and its cooperation with private U.S. IT-corporations such as Google and Facebook”.
“Drawing specifically on the NSA Prism program, the presentation offers law enforcement, intelligence and other interested parties, to join an alliance in order to establish equivalent data-mining operations in Russia,” it adds, sticking its boot firmly back into U.S. government mass surveillance programs.
yogaesoteric
December 1, 2017
Also available in:

